Verkada Access Control and Video Security: Real-Time Monitoring and Incident Response
When it comes to monitoring and managing a building or physical space, teams rely on various solutions to effectively detect and understand events happening across their organization. For most, this begins with video security and often coincides with a physical access control system.
While both of these solutions play an essential role in providing teams with greater visibility and management of their space, using them together can be a serious challenge. They are often used as fragmented systems that typically add more overhead and complexity to any monitoring solution. Combine that with a need to handle incidents in real-time, many solutions on the market make this troublesome if not impossible.
Below, we explore how access control and video security solutions can work together and how Verkada’s native integration provides real-time visibility into door-based events happening across an organization.
(Not Always) A Perfect Pair
When thinking of a physical security system’s components and how they play a key role in investigations, its no wonder access control and video security tend to go hand-in-hand.
Users can see all door-based activity with an access control system, including the event type, location, and credential used. However, a credential only tells part of the story, and not necessarily a means of truth for who accessed—or attempted to access—a door.
Understandably, a video security system would appear to be the perfect puzzle piece for this missing information. Unfortunately, it isn’t always the right fit.
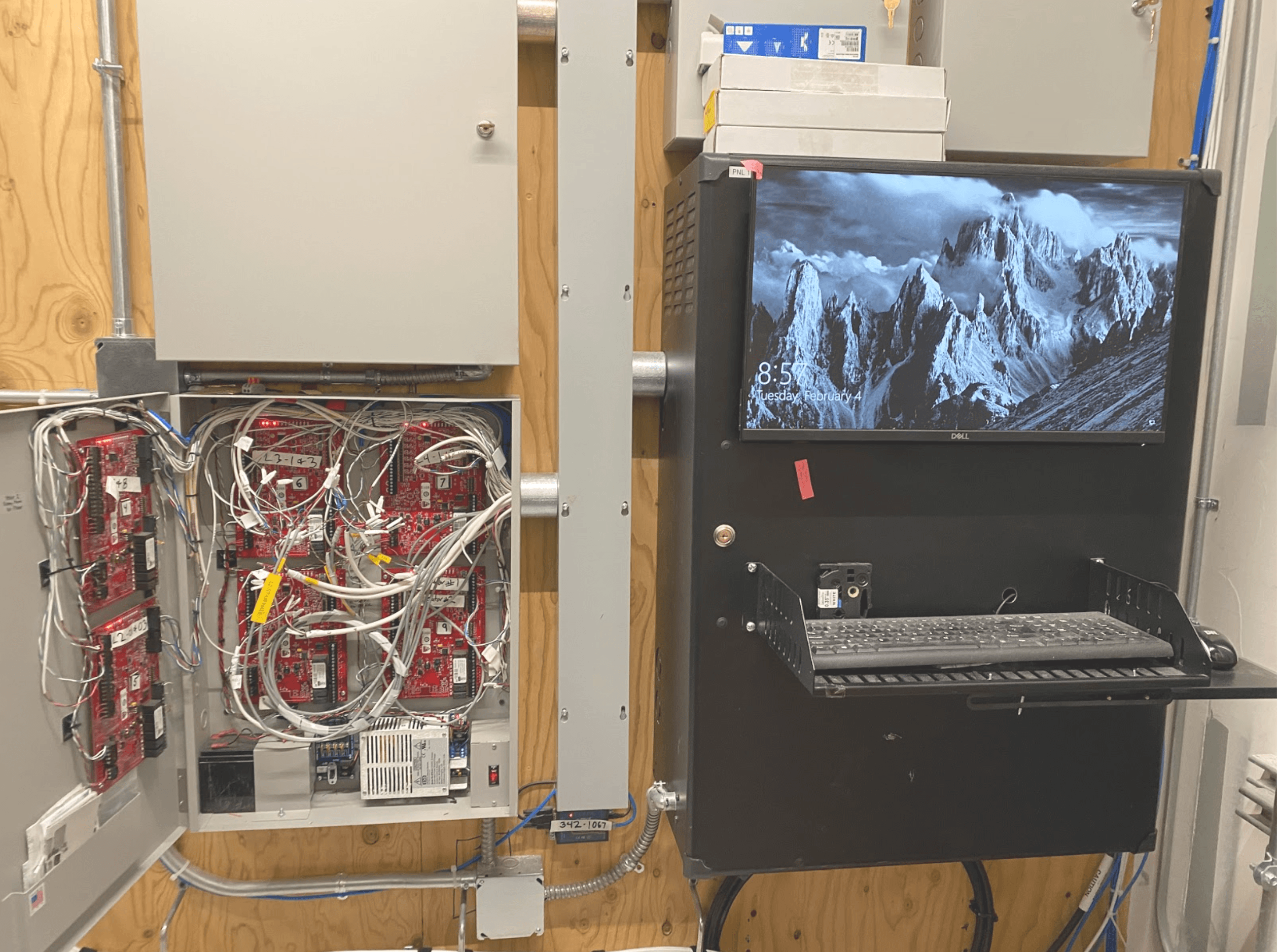
The challenge starts with the solutions themselves. Many traditional video security and access control systems were not designed or built to work together, meaning even solutions from the same vendor may require that users have access to separate management systems. This is especially true for access control, which historically is managed from a local machine found in places like server rooms.
These deployments make it difficult and time-consuming to gather necessary information, as users need to document key events and go back-and-forth between platforms. In many cases, this results in teams deciding to forgo collecting information regarding access-based events for many investigations.
Users can also experience difficulty accessing and managing events for solutions that use another management platform to integrate two or more physical security systems.
These integrations can lead to limited access to certain features that may be part of the product on its own, leading to teams having to sacrifice convenience over functionality. Or even more frustrating, having to still go back-and-forth between platforms.
Beyond functionality, there is also the challenge of the complexity of the configuration of these integrations. Getting two systems to work together isn’t something that any ordinary and even advanced user can set up on their own. It can require a deep understanding of networking and implementing these systems, which can be troublesome and costly to set up and maintain.
Verkada Access Control: Bringing It All Together
While it is possible to use separate access control and video security solutions together, the ideal system is one that natively integrates door-based events with corresponding video footage. At Verkada, we’ve taken an approach to building a centralized management platform that enables users to use both access control and video security without sacrificing one or the other.
This is all made possible by Verkada’s web-based Command platform. Users can access their organization from any web browser or smartphone, and instantly monitor events happening across their organization.
It starts with a simple integration between Verkada Access Control and Security Cameras. With just a few clicks, users can effortlessly associate a camera with any door in their organization.
Since the cameras and doors exist in the same platform, historical door-based events are automatically connected to the associated video footage. From there, users can simply choose any door-based event and instantly see the corresponding video.
Users can further investigate a situation by adding additional cameras to see what happened following the event, allowing investigators to see further how a situation unfolded. From there, users can archive footage and share it with any necessary parties, just like they would doing a video-based investigation.
Additionally, beyond credential-based events, this all-in-one experience allows teams to monitor situations where a key card or credential wasn’t present, such as opening a door from the inside. Users can easily see these events in real-time using the Verkada Access Control Live feature, which provides a feed of door-based events and corresponding footage happening across an organization.
With more traditional access control solutions, these types of events would likely go undetected. By having video footage with these moments, teams can quickly detect if something needs further attention and potentially identify and resolve incidents before something happens.
Teams can also monitor for incidents where a door is forced or held open. These types of situations can be critical to the safety and security of others. With traditional access control solutions, the validity of this type of event can be brought into question. At the same time, with Verkada Access Control, users can see the event that took place and who was involved.
Evaluating Your Options
There are many varying factors that can go into determining the right physical security solution for your organization. For many, having access control and video security systems that work well together is critical to providing the safest environment possible.
Understanding the limitations, as well as the requirements of the many solutions out there is a key part of any solution evaluation. In order to determine what is best for your organization, consider the following:
How am I currently using access control today for investigations?
How does my existing access control and video security solutions work together to help resolve incidents?
How much time do I need to successfully investigate an incident?
Who will use these tools and how will they be able to use the solution I choose?
If you’re interested in learning more about Verkada Access Control and its native integration with video security, sign up for our exclusive webinar or contact [email protected] for more information.






