Why Your NVR Is Probably Less Secure than a Hybrid Cloud Video Surveillance Solution
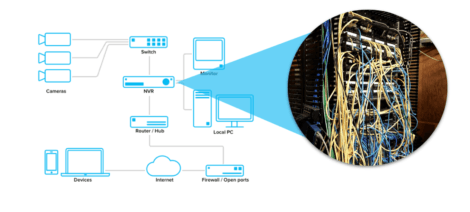
Video security systems have traditionally relied on a network video recorder (NVR) to capture footage. These devices, which serve as a central hub connecting an array of cameras, have long been billed as a highly secure system.
Although this reputation persists, it is largely unearned. NVRs, as well as digital video recorders (DVRs), are now routinely attacked and fail to provide anything close to the level of protection most IT professionals expect.
The “secure NVR” myth comes from the fact that an actual, air-gapped NVR is indeed incredibly secure. But this is less a function of specific equipment capabilities and more due to the fact that almost any device that is cut off from the wider network will be challenging for hackers to exploit.
NVRs: Only Secure in Theory
Unfortunately, few enterprises use NVRs in this manner. Most modern companies will want to have remote access to their footage. Whether for monitoring in real time at a central location or simply transferring archives of individual incidents, this is usually a must-have feature.
Some very small organizations may just want a single screen, or cluster of screens, for on-site viewing. But, by and large, even most small businesses—and especially larger corporations with multiple locations—will want a way to access what is being captured off site.
As soon as an NVR is connected to a network, vulnerabilities are introduced. Doing so requires opening or forwarding ports not to mention establishing a VPN, which are exploited by hackers all the time.
Attacks Are Common
In recent years, we have seen a trend of hackers targeting video cameras and NVRs. A NUUO brand NVR was targeted by the Reaper IoT Botnet in 2017, for example, and the exploit reportedly opened up the system’s cameras to similar botnet attacks.
This year, security research firm Tenable also found an exploit called Peekaboo that could affect the company’s NVRMini2 model. “Once exploited, Peekaboo would give cybercriminals access to the control management system, exposing the credentials for all connected video surveillance cameras,” wrote Tenable. “Using root access on the NVRMini2 device, cybercriminals could disconnect the live feeds and tamper with security footage.”
Disconcertingly, it isn’t just NVRs. Video cameras from certain manufacturers have proven unreliable as well. The U.S. Senate deemed the risk significant enough that it barred the federal government from using cameras from manufacturers Hikvision, Dahua and Hytera Technologies.
As codified in the 2019 National Defense Authorization Act, agencies are now prohibited from buying any surveillance equipment from these brands for the sake of “public safety, security of government facilities, physical security surveillance of critical infrastructure and other national security purposes.”
Poor Vigilance, Slow Updates
The confusion between reputation and reality is another key reason that NVRs can actually be less secure than other options. Many veteran IT workers who may have started working with video surveillance decades ago have fallen for the this security fallacy. Consequently, they don’t practice the same level of vigilance that they would when working with a modern, cloud-based surveillance solution.
Less vigilance leads to slower reaction times. Blinded by this false sense of security, operators tend to be lax about detecting vulnerabilities and installing critical firmware updates.
In practice, this typically makes the alternative much more secure. Most IT departments have moved on from the notion that anything connected to the internet will ever be 100% secure. Instead, they recognize that some level of risk will always exist, prioritize quick reaction times to mitigate known exposures and continually look for new vulnerabilities.
Hybrid Cloud Advantages
While the traditional NVR option is falling out of favor among today’s security pros, for more than just security reasons, there are other options. Cloud-based alternatives, while once held back by security fears, are now being seen as having several differentiating advantages.
Learn more about hybrid cloud video surveillance in our next webinar
In the case of Verkada, for example, the company provides ongoing support for clients with its team of security experts and constant penetration testing. Given everything the company has at stake, it is much more likely to stay on top of vulnerabilities than any single organization’s IT team.
Moreover, Verkada’s cloud-based cameras use advanced, encrypted in transit and at-rest and in transit. Transport security is provided by TLS 1.2. As for stored video, each camera is associated with a unique RSA keypair. The cameras are issued a public key, which they use to encrypt video and the private key is encrypted with AWS KMS before being stored.
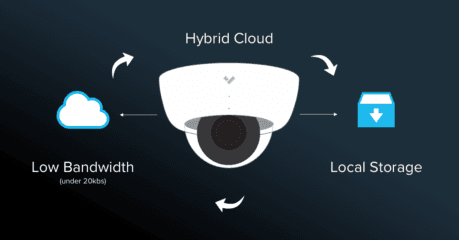
These cameras and have outbound-only connections, drastically reducing the possibility of any unauthorized users accessing the network. Video security solutions that are built with security in mind from the ground up, have significant advantages over NVRs.
When you put it all together, the rationale for using hybrid cloud systems becomes clear. While the public relations for NVRs can talk a good game, they ultimately cannot live up to their reputation.
—
For additional information about this topic, check out our latest eBook, How to Choose the Right Video Security System for your Organization.





