Introducing Passkeys, Temporary Users, and Enhanced Session Controls
We've built tools and features in Verkada Command to make it easy for our customers to control who has access to their security platform and what permissions those users have. Today, we're introducing three new features in Command that enhance these security and privacy controls:
Passkeys for more secure and faster login
Temporary user accounts for installers, contractors, and support staff
More granular policies for user sessions
Log in with a fingerprint, face scan, or security key
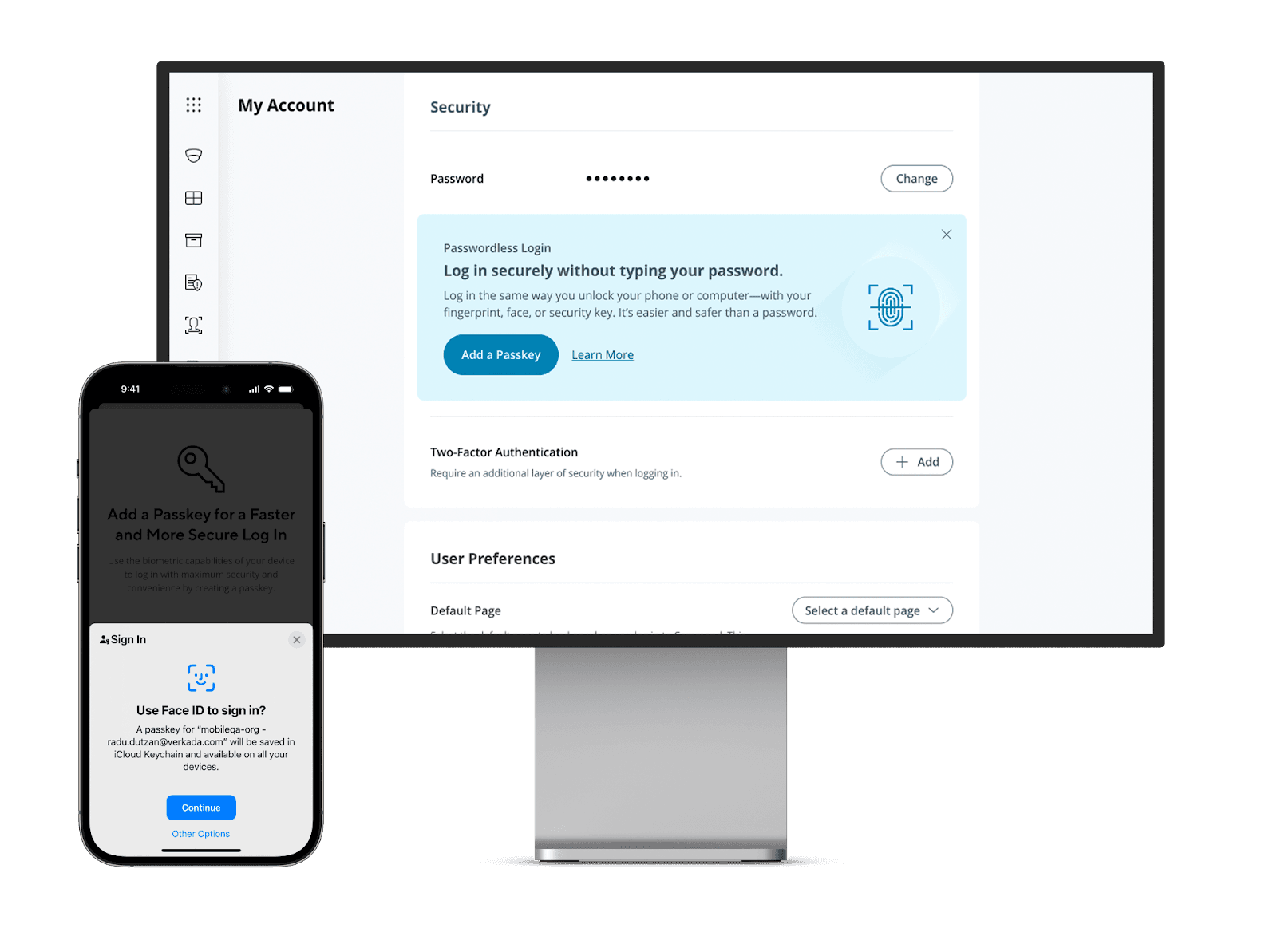
Given the sensitive nature of the data that customers store, view, and interact with in their Command organizations, it is crucial to make Command access as secure as possible. And that means joining the industry-wide move toward passkeys.
Users can now log into Command the same way they unlock their banking and other high security apps: with a fingerprint, a face scan, or security key. Compared to passwords, these methods are both simpler and more secure, and they’re resistant to online attacks like phishing. With passkeys, users can sign in without even typing in their email or organization name, allowing them to access Command faster in case of an emergency. Org Admins have the option to enable or disable passkey login for all Command users.
Create temporary user accounts
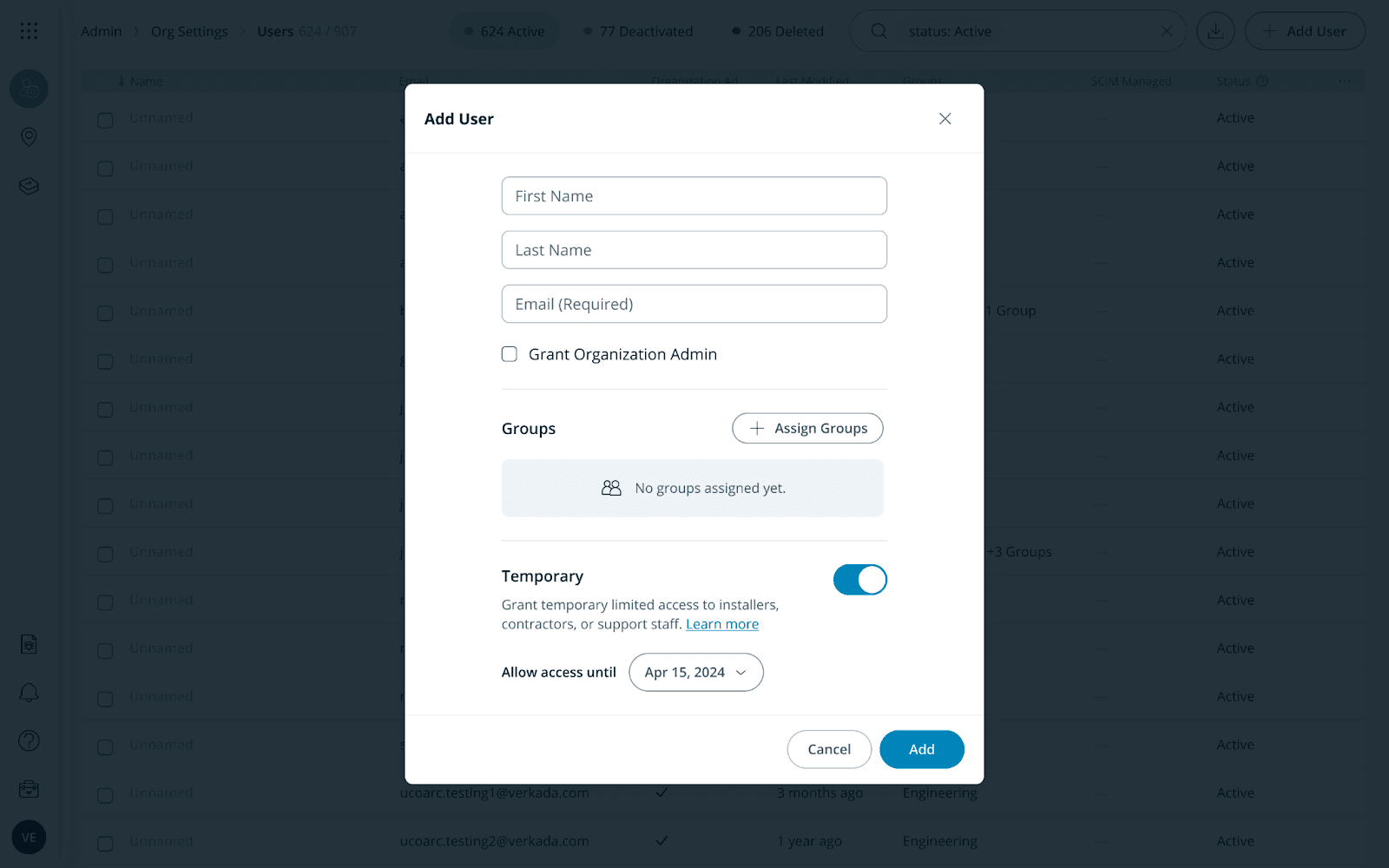
Many of our customers receive help from installers to set up their Command environment. In order for installers to add devices to Command, they need to be added as a user and given at least Site Admin permissions. And for actions like configuring floorplans and creating new sites, installers need to be given Org Admin permissions.
To address this use case, we're introducing temporary user accounts. Temporary users can be assigned any role within Command, such as Site Admin or Org Admin, but only for a predetermined time period. At the end of this period, their Command access will automatically expire. Temporary users can be extended, reactivated, or converted to regular users (and vice versa).
To further protect customer privacy, we’ve put in place guardrails around sensitive actions for temporary users. Regardless of their assigned roles, temporary users are not able to export or download any information from Command. This includes but is not limited to camera footage, audit logs, and user information. In addition, temporary users are not able to generate support tokens or accept terms and conditions on behalf of the organization to enable features like People Analytics. For more details, please refer to this Knowledge Base article.
Apply more granular session policies
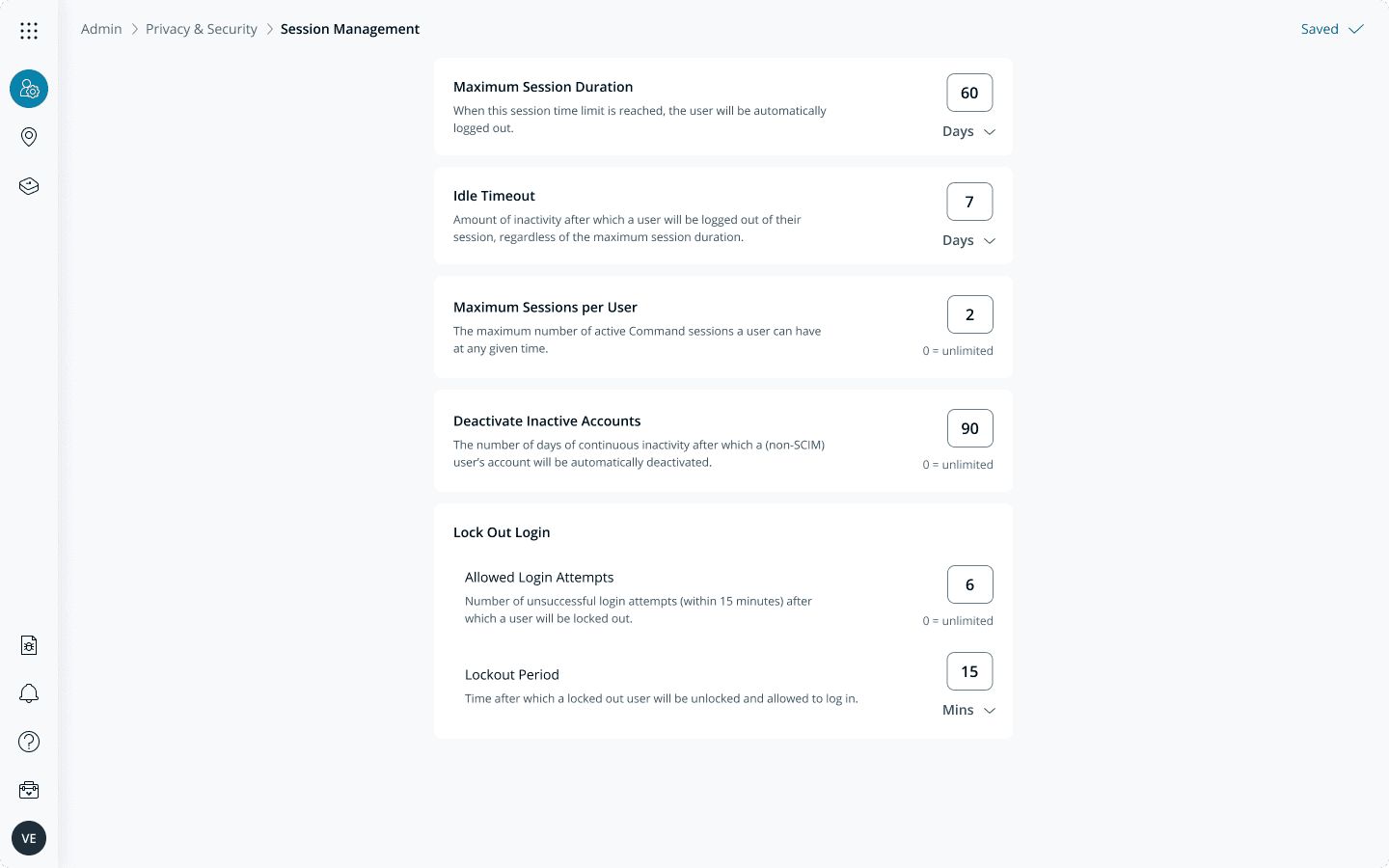
Another way in which we are strengthening application security is providing more robust session management tools. Org Admins can now set more granular policies such as maximum session duration, idle timeout, maximum concurrent sessions, and maximum login attempts. These policies help customers protect user data, prevent unauthorized access, and mitigate session-related vulnerabilities.
Get started
All of these features will be available to customers on February 22nd. To learn more, please see our knowledge base articles on passkey login, temporary users, and session management.






